Data Security. We all need to deal with it. There are many tried and true ways of doing things. Many of the problems you'll encounter have been solved. Some of them will require creative thinking. All require a basic understanding of the difference between big thing and little thing. Not everyone possesses the ability to differentiate between the two.
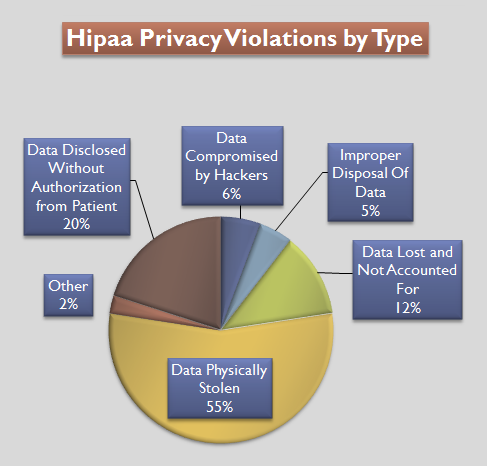
R.J. works for a health insurance company. These folks have access to some of our most private information, and take HIPAA regulations to secure and protect it quite seriously. Any breach of security requires notifying customers of potential exposure, as well as reporting to government imps bureaucrats better not dealt with. Naturally, the bean counters from the board on down all repeat the mantra of protecting the customer data at all costs.
The team that employs R.J. developed the phone menu system. You're familiar with these beasts; they're designed to teach you Zen levels of patience while you try to do something, anything, while preventing you from having contact with a human. To that end, they allow you to perform all manner of tasks, provided you can stumble through the maze to the right sub-menu, and enter the magic code(s).
One day, while snoozing on his bus ride home, R.J. got an emergency email entitled Potential Personal Health Information Exposure. As he grudgingly opened the email, the familiar Star Trek red-alert security-whoop sounded. The mail details stated that every enterprise level team (e.g.: all of them) had to be on an emergency call immediately! Wanting to be a good Red Shirt, R.J. jumped onto the call.
Unfortunately, along with 9 levels of management, all in full panic mode, there was only one other person on the call; a DBA.
After 15 minutes of managers pouring gas on the fire and assuring each other that there was plenty to panic about, the DBA got a moment to talk. There wasn't an actual data breach and no information had been affected or viewed. As part of a routine audit, the DBAs had discovered that a determined individual could find out that member id nnnnnnnnn had a birthday of yyyy-mm-dd. The DBAs already had a fix and just wanted to let the consumers of the data (e.g.: R.J., and all the other teams that hadn't joined the call) know that the affected data would be unavailable for a few hours while they applied their change.
This set the managers off on a rant that could only be had if you were a manager:
Mgr: What if someone gets the data before the fix can be applied? DBA: That's why we've already taken it off line (until we can apply the patch) Mgr: But what if they get to it anyway? DBA: It's off line - it's inaccessible to anyone Mgr: But you can access it, so other people can too! DBA: No, off line means OFF LINE; I work here and have privilege, others don't Mgr: Someone get Legal on this call! ...
...and downhill it went from there.
After 15 more minutes of this, R.J. had reached his stop, and disembarked both call and bus, secure in the knowledge he could sleep in peace.
The next day is when the fun really started. The DBAs had fixed the potential problem and all was well. In Techno-Land. But managers, especially the C** variety, don't live there....
The memos flew fast and furious about data security being of paramount importance. Everyone, with no exceptions (except the high level managers, of course) was required to take the HIPAA and internal data security training courses - again. Committees (of managers) were formed to assess what needed to be done, and spec out the work and cost.
All for a problem that had been identified and fixed before it was even noticed by anyone.
image source