In the early 2000s, Fernando was the Network Operations Manager for a wireless ISP known for its comprehensive customer support. They had techs who’d install the necessary gear, and consultants who’d arrive onsite to reconfigure computers, routers, firewalls, and everything else, until the customer was completely up and running. A small team of developers could even custom-build any small software apps a customer might ask for.
The service was well loved. In fact, it was so thorough and helpful that after the initial install hiccups were soothed, Fernando and his support team almost never heard from customers again.
“We’re too good!” a sales manager complained during one of the most surreal meetings of Fernando’s career. “We’re hurting our own business! There’s gotta be a way for us to drive up service calls!”
“Ethically,” another sales-beast added quietly.
“Right, ethically. What can we do?”
Brainstorming commenced. A set number of service calls that the customer had to pay for upfront, whether or not they were ever used? Quarterly “check-ins” built into everyone’s service contracts (at a price, of course)?
“Hang on, this is still about helping our customers, right? Or at least it should be,” Fernando said. “What’s one thing that everyone needs help with, all the time? Security. New threats pop up all the time. Why don’t we set up a listserv that we can use to recommend security updates and best practices? That way, we’re staying in touch with the users with good advice—and we can encourage them to call us for help with implementing that stuff.”
It was a fantastic suggestion. The sales managers were happy. The top-level execs were happy. And since it had been Fernando’s big idea, he had the privilege of implementing it. He set up a Majordomo list-server, configured to accept postings from his email address only, then carried out his plan to great success. Customers received highlights from Bugtraq and other relevant sources, generated steady business, and were protected from many nasty problems.
Everyone was thrilled.
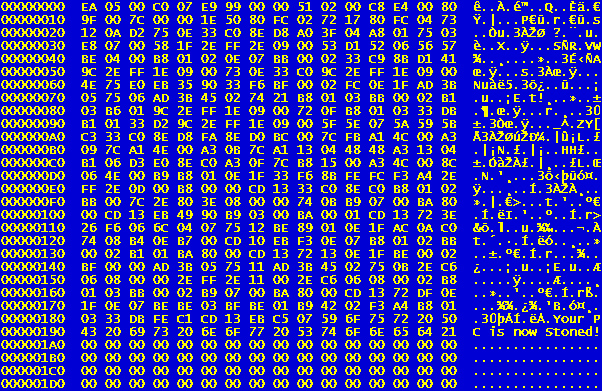
It took a full two years before the storm clouds surfaced, but surface they did. Bafflingly, Fernando received an email from the listserv that he hadn’t sent. He opened it, and slowly realized what he was looking at. A Windows virus from some customer's site had replied to one of his emails, and had used his email address as the forged sender. His list-server had then dutifully forwarded it to the entire distribution list.
Horror shot through him. Not two seconds later, the phone rang.
“Hi Fernando, it’s Brian. Listen, I just got your email. What do you need me to do with this here?”
“I’m sorry, it was a mistake,” Fernando gunned out, heart pounding. “Please go ahead and delete that.”
He was hardly off the first call when the next one came in. While he was on the line, he watched emails pile up in his inbox.
I don't understand what you mean by this.
Am I supposed to install this?
Can you have one of your guys come out and install this for me?
Fernando shook with terror. Sweat beaded at the nape of his neck. Hundreds of customers could potentially infect and torpedo their own operations, all because the Network Operations Manager in charge of security emails had just sent out a virus.
The next free moment on the phone, he called his receptionist. “Hold all my calls for the next few minutes, please.”
Before he heard any acknowledgement, he dropped the phone back into its cradle and began drafting a clarification email to explain the whole mess. Please disregard—
“Hey, what was that weird file you sent out?” A coworker leaned lazily past his office door. “Looks kinda suspicious to me.”
“I’m aware of that.” Fernando struggled not to curse or yell. “We’ll talk later.”
Once he’d sent out the email, he firewalled the majordomo process to only accept email from localhost. Then he sat back, closed his eyes, and prayed.
His quick action made more of a difference than any divine intervention. Fernando never heard any reports of customer systems getting infected from that incident.
Disturbingly, he also never figured out whose machine had sent the original.